The Smartest Financial Choice for VDI Replacement
Workspot is an intelligent, purpose-built platform that unifies Enterprise Browser, DaaS, and DEX to radically reduce your VDI costs by up to 90%
Workspot helps you…
Save 90% with Enterprise Browser
For users who need access to web applications, simply use our Enterprise Browser and eliminate VDI infrastructure
Save 80% with DaaS & AI
Control cloud infrastructure cost with intelligent just-in-time and just-enough provisioning on your cloud of choice – AWS, Azure, and GCP
Become an IT Hero
Make happy users and a happy CFO with alerts and observability that’s built-in, not bolted on.
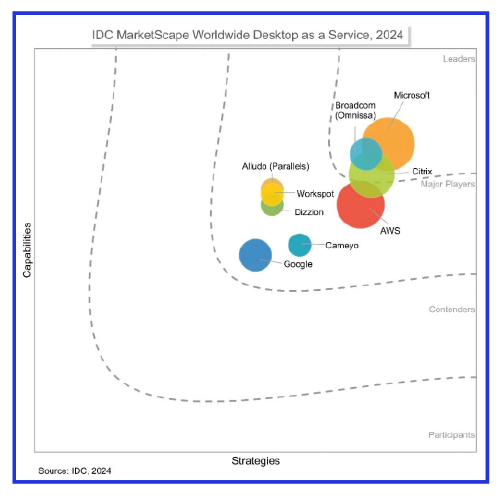
Workspot Named a Major Player in IDC MarketScape for Worldwide Desktop as a Service 2024
Learn why Workspot is suited to providing desktop as a service to all businesses and a consistent, managed desktop experience delivered at a clearly stated cost, making it accessible even for organizations with limited virtualization expertise.
Save up to 80% with DaaS + AI
Your data center is provisioned for peak usage and has average 12-18% utilization rate. With Workspot DaaS and AI, you can take advantage of AI and consumption billing in the cloud to reduce cost by 80% while delivering great end user experiences.
- Just-in-time Provisioning
- Just-enough Provisioning
- Fine-tuned Costs
The Workspot Enterprise Browser — Secure, Cost-Effective Access to Enterprise Web Apps
If your users primarily need secure access to a few web apps, why pay for a full virtual desktop? The Workspot Enterprise Browser is a low-cost, highly secure solution designed for unmanaged, untrusted, or BYO devices. It enables seamless access to SaaS and private web apps while ensuring IT-controlled security, data protection, and compliance.
Discover how you can reduce costs, enhance security, and simplify access for your workforce.

Manage the Complete Deployment Lifecycle
Does your organization have all the cloud and VDI skills? Is your infrastructure team retiring from the workforce? Our Customer Success and Support teams can be your expert cloud and VDI partners in the entire deployment lifecycle, including implementation, integration, user testing, adoption, and production support.
High-Performance 3D CAD in the Cloud
Are you struggling with data synchronization issues with distributed engineering teams? Our customers have centralized their data and compute into a few regions in the cloud and deliver exceptional user experiences anywhere in the world.
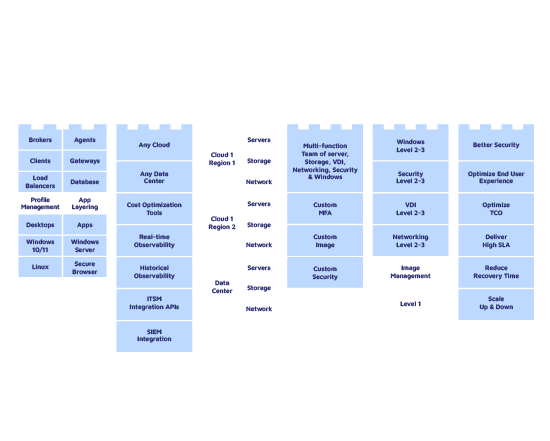
Powerful, Resilient Platform
One unified platform that gives you total freedom of choice, puts observability front and center, and reduces total cost of ownership.
Proven Use Cases
Secure your remote and hybrid work strategy, modernize your VDI infrastructure, strengthen zero trust security, and address a broad range of use cases.
Industry Focused
If security, collaboration performance, and reliability are at the forefront of your enterprise, Workspot has you covered.
Trusted by
Meet a few of our customers across different sectors.
Get started today

See Workspot in action
Have one of our expert team take you through a live demo and answer any questions you may have.
Get a Demo
Contact us today
There’s a better way to learn about us. Talk to our team and get the answers you need, fast.
Contact us
Join our community
Share and receive the latest and greatest information on all things Workspot. Explore our events, join our Slack conversations, view our knowledge base, and more.
Our Community