It’s not surprising that organizations of all sizes are rethinking approaches to information security. The statistics on cybercrime are stunning: Cybersecurity Ventures forecasts that cybercrime will cost the world more than $6 trillion annually by 2021. That was back in 2016, and by all accounts, their prediction is being proven out. Cybercrime – especially ransomware – is the fastest growing crime in the U.S., and the attacks are increasing in number, scope and sophistication.
The magnitude of the problem requires IT leaders to think completely differently about how they protect corporate apps and data. This is where the concept of “Zero Trust” applies, and it goes well beyond the old “protect-the-perimeter” way of thinking. In a world where people use multiple endpoints every day and are constantly on-the-move, the attack surface is way bigger than it has ever been. Sure, the perimeter needs to be protected, but even good employees go bad, or they do dumb things – like losing a laptop in the airport. A Zero Trust model essentially means that no one is trusted, either outside or inside the organization, until their identity is proven and the conditions under which they want to connect to corporate systems are known. At that point, just the right level of access can be granted for the user in a particular context.
Workspot and Zero Trust
Among the many benefits of cloud desktops – including less IT complexity and greater business agility – is the opportunity to improve the company’s information security posture. Achieving Zero Trust demands both process changes and smart technology choices. At this point, most CIOs believe that the major cloud providers can offer a stronger defense against security breaches than in-house IT teams can implement for on-premises infrastructure. While this confidence has opened the floodgates for moving workloads to the cloud, the security implications of doing so must still be carefully considered. As we help enterprises navigate the approaches to cloud desktops, one thing is very clear – cloud desktop solutions are not created equal, and understanding the nuances, especially when it comes to the underlying architecture, can have profound consequences on data security, the success of the cloud desktop project, and more importantly, the level of risk faced by the organization.
The following are the primary ways Workspot cloud desktops on Microsoft Azure strengthen information security and help protect your organization from cybercrime. Make sure you drill down on these topics with the vendors you evaluate!
Principle of Least Privilege (POLP)
Generally, POLP applies to processes and people. In our world, when we think of POLP, we are referring to how Workspot’s cloud-native architecture allows us to deploy cloud desktops, apps, and workstations in a way that protects PII and our customers’ data. It’s an architecture conversation, and it’s crucial that you have it with VDI vendors you are evaluating. When we built our solution, we separated the control plane from the data plane. In practice what this means is that once the user has been authenticated and the session established, the user accesses virtual resources directly from the cloud. Unlike other vendors’ solutions, our customers’ application data does not enter, nor is it ever stored, in our control plane. It stays tucked away in the customers’ Azure instance. In the context of Zero Trust, trusting no one, either inside or outside the organization, includes the vendor running your virtual desktops! As we have said many times when it comes to cloud desktops, architecture is everything, so dive deeply into this topic so you know exactly where your data is.
Conditional Access
As we’ve said, we apply POLP to our architecture and how we deploy cloud desktops for our customers (that’s our secret sauce!). But what about people? How do you defend against bad actors and people who just make a mistake that results in a security compromise? At a high level, this is all about proving a user’s identity and then providing access based on the context of the user’s situation. What is the user’s role? What do they need to accomplish? Where are they located? What device are they using? What network are they on? Based on this context, IT can set and enforce policies around what actions the user can take. Given the context, should they have access at all? Should they be allowed to print? Or take a screenshot? Should an upload from this device be allowed? And more… Operating in a Zero Trust world means that everyone is guilty until proven innocent, and that requires a new way of thinking about information security.
Multi-factor Authentication (MFA)
As consumers, we see MFA being increasingly used as we access a variety of online services. It should be no different for businesses of all sizes because bad actors target large and small businesses alike. Anytime there is data and IP to protect, you need MFA. At a conference we recently attended, MFA was top of mind for a group of IT leaders. Workspot was built for enterprise deployments, and among other things, that means we integrate with the authentication systems you may already use or are evaluating. The majority of our customers use Azure AD, Azure MFA, Okta, Duo and/or PingID.
Better Visibility for IT
If IT teams can’t properly monitor what’s going on with users and desktops, it will be pretty tough to identify risk or an actual breach. Good visibility begins with a single pane of glass to monitor and manage all cloud desktops, workstations and apps globally. Additionally, Workspot’s solution is instrumented at all points, including the client (the user’s workspace), the gateways they traverse and their cloud desktops, so every time the user acts, data is collected about that interaction. A real-time events feed of all user activity provides IT an at-a-glance view to the state of the operation. Additionally, our Network Operations Center team has end to end visibility and can help identify any trouble spots – even those that go beyond Workspot’s solution – and can help recognize patterns that might spell risk.
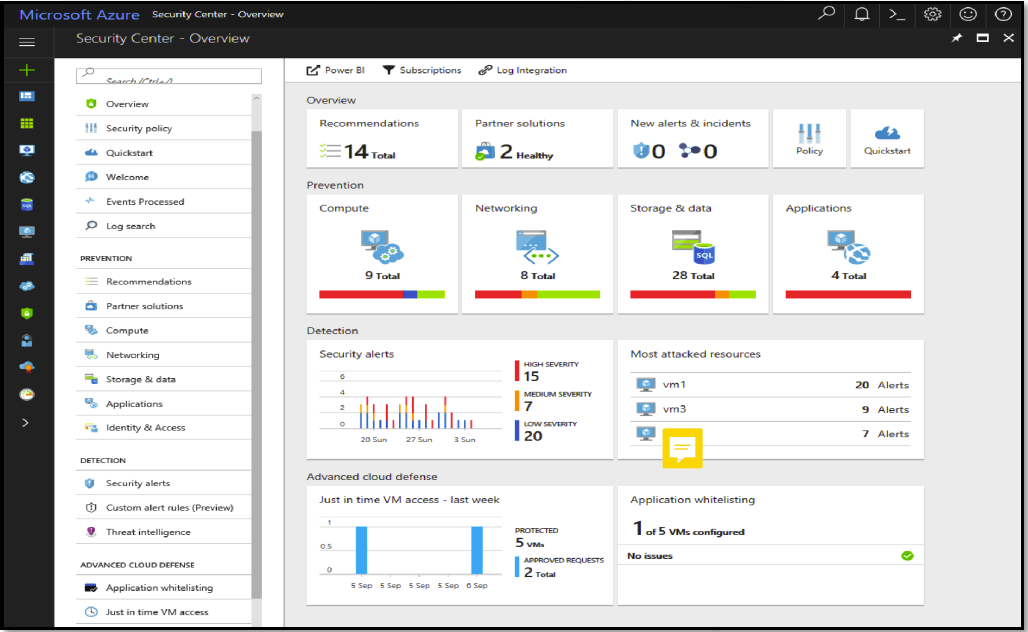
Microsoft Azure Security
Keeping your corporate information safe is a joint effort between the customer, Workspot and Microsoft. In this age of heightened risk, with more frequent attacks that constantly evolve in their sophistication, it’s an all hands on deck effort to secure information assets. Microsoft has invested billions of dollars into security, including the Azure platform. Workspot leverages the strength of those security investments by using Azure Security Center to gain deep visibility into all activities in a customer’s cloud desktop subscription, across Azure regions worldwide.
Take Action: “Only the Paranoid Survive”
Andy Grove, founder and former CEO of Intel, gave us these words of wisdom. Although he intended it as a business management strategy, it applies to information security as well. CIOs and CISOs cannot be complacent just because they’ve escaped being affected by a security breach thus far. The next attempt from a hacker to benefit by gaining access to your information assets is just around the corner, and a good dose of paranoia, if it compels you to take action that leads to a stronger security posture, is definitely a good thing. Workspot’s inherently secure cloud desktop architecture, combined with Microsoft Azure, is a powerful element of your Zero Trust initiative.
Ready to learn more? Schedule a demo and let’s explore your requirements.
Cloud PC Security




